Linux comes with a plethora of network utilities to choose from. tcpdump is one of those powerful networking tools that can capture and analyze network traffic if you need to troubleshoot network errors in Linux.
Let’s take a look at the tcpdump command and explore how to use it to capture network traffic.
Installing tcpdump on Linux
tcpdump is usually pre-installed with all common Linux distributions and security-based alternatives. So you should be able to use it immediately by typing tcpdump with a sudo prefix.
If you are unable to run the tcpdump command and are stuck on the “tcpdump: command not found“, let’s learn how to install tcpdump on your Linux machine.
To install tcpdump, launch the terminal and run the command for the Linux distribution you are currently using:
On Debian/Ubuntu derivatives run:
sudo apt-get install tcpdumpOn Arch-based systems run:
sudo pacman -S tcpdump
To install the tcpdump utility on Fedora, CentOS, and RHEL, run the following command:
sudo dnf install tcpdumpNote that if you are prompted to install libcaptype Yes Where Yes because it is a core dependency, without which tcpdump will refuse to start. This should install the tcpdump utility and resolve the “command not found” error.
Now that tcpdump has been installed on your system, let’s explore the different options and features it offers.
Capture network traffic with tcpdump
tcpdump has many flags to modify its execution, but it can also be run as a standalone command. However, running tcpdump without any flags or arguments would be to neglect its full potential. It’s always better to use a few flags to adjust the execution and output if needed.
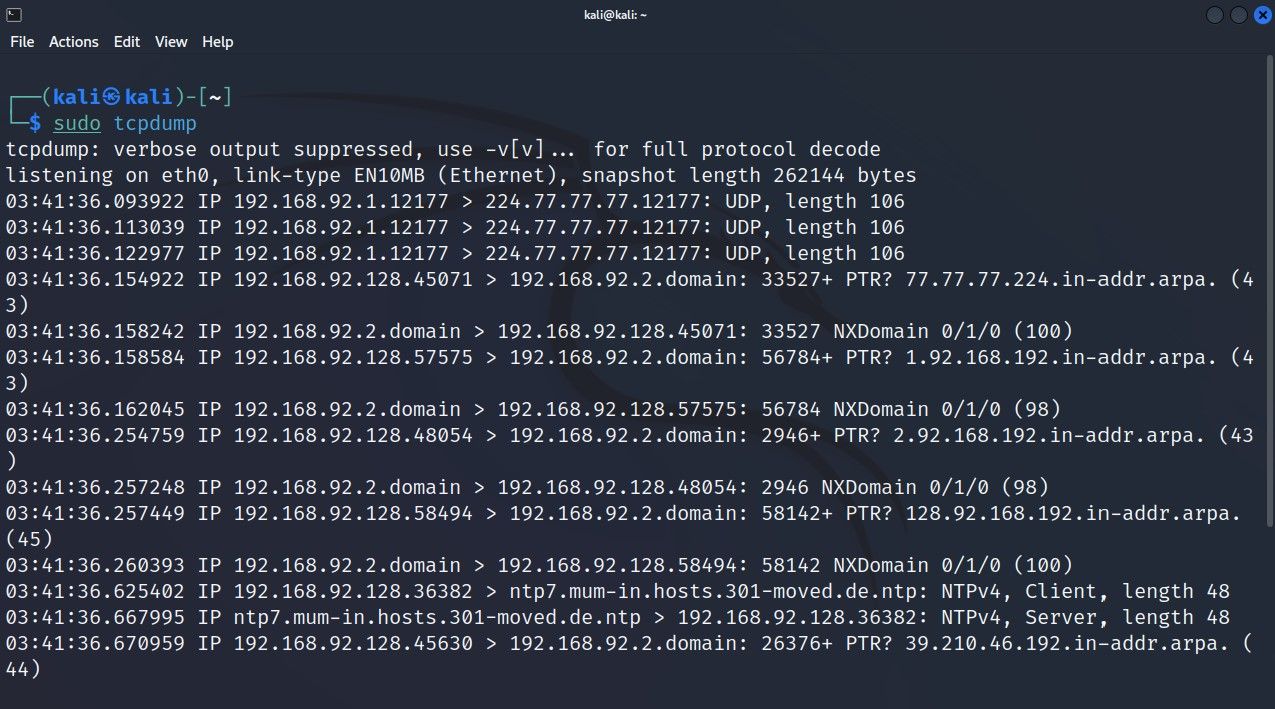
Type this command to monitor network transmissions with tcpdump:
sudo tcpdumpNow tcpdump will start capturing network packets automatically until a break signal is sent with CTRL+Z to interrupt the process manually. To limit the total number of packets captured, use the -vs flag and type the desired packet limit next to it:
sudo tcpdump -c 5If you can’t make sense of the output at this time, you should first familiarize yourself with the tcpdump output format.
Check available network interfaces with tcpdump
By default, tcpdump captures traffic from any available network interface. If you are using multiple active network interfaces, you may want to define the network interface from which tcpdump should capture packets. To start tcpdump on a specific interface, you will first need to know the interface name.
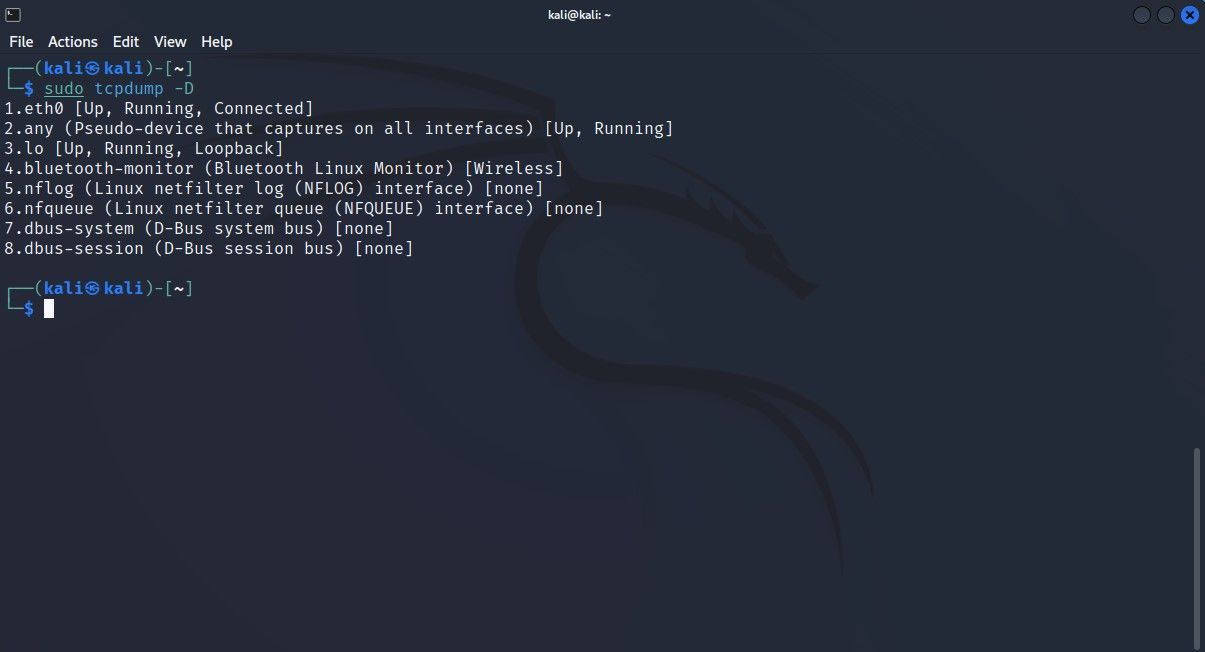
Here is how to list all available network interfaces with tcpdump:
sudo tcpdump -DOr, you can add the –list-interfaces flag to command:
sudo tcpdump --list-interfacesThe returned output contains a list of all active network interfaces that tcpdump can listen on. To configure tcpdump to capture transmissions from a particular network interface, enter this command:
sudo tcpdump -i interface_idOr, you can add the –interface flag to command:
sudo tcpdump --interface interface_idNow that we’ve captured a few packets, let’s take a closer look at them and learn how you can modify the output to make it more readable.
Explore tcpdump filters
tcpdump is capable of capturing an overwhelming amount of traffic in a single run. Such information overload can confuse you when investigating or troubleshooting issues with a specific host or network protocol.
This is where tcpdump filters come in. You can add tcpdump command with some flags to filter network traffic and capture specific packets. You can then store these packets and analyze them later to get to the root of any network-related problem. Let’s learn how to use filters in tcpdump.
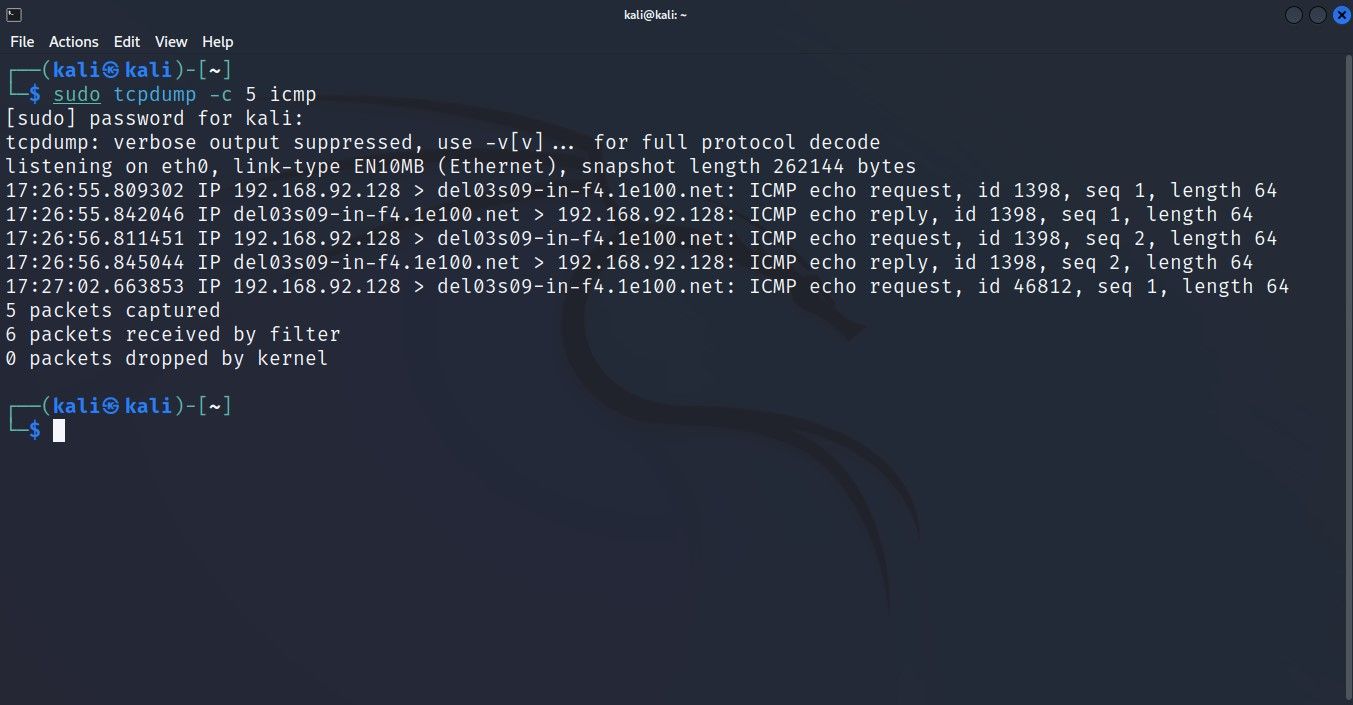
Filter packets according to the network protocol used
To filter packets transmitted via a specific protocol, type the protocol name with the tcpdump command, and it will only capture packets traveling via the defined network protocol.
For example, to capture ICMP-based packets, you just need to attach ICMP at the end of the tcpdump command. The process is the same whether you want to capture only UDP or TCP packets.
sudo tcpdump -c 5 icmpThis command will only return output if there is data exchange via the ICMP protocol.
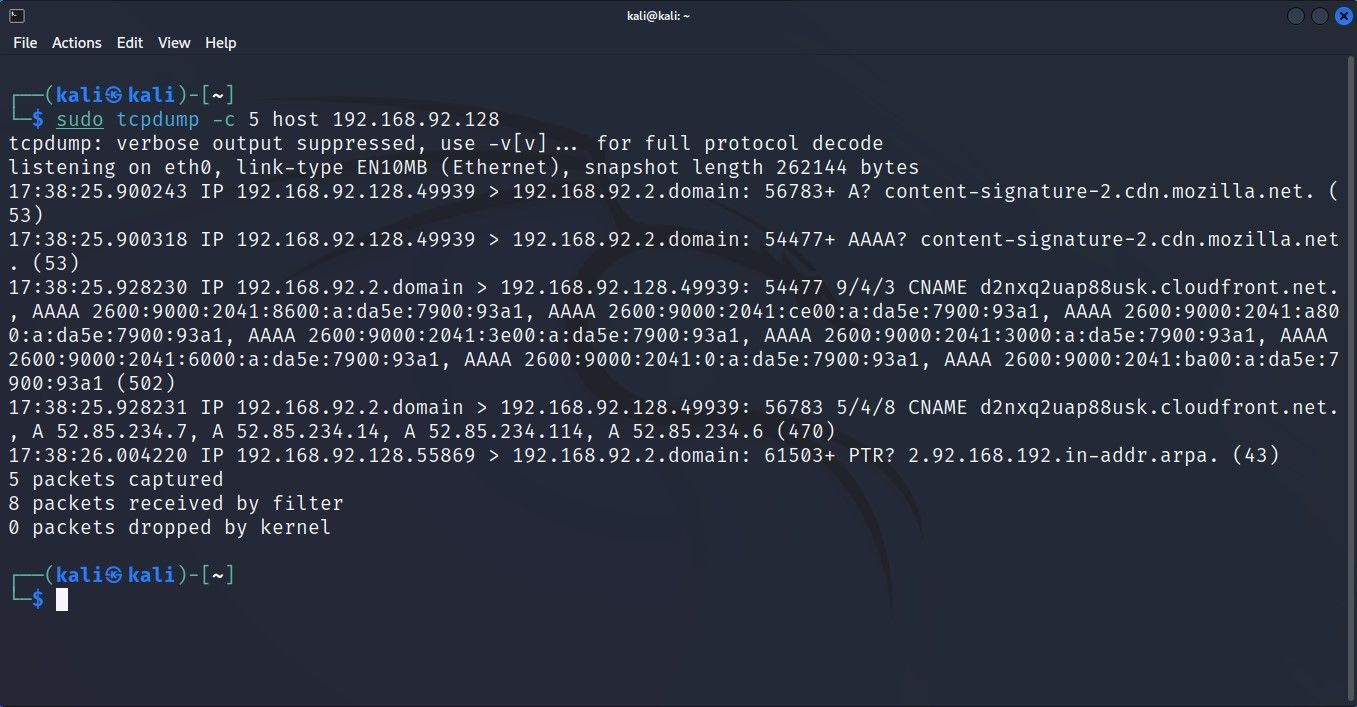
Filter packets based on host
You can configure tcpdump to capture packets related to a single host with the host setting. This is especially useful when all systems on your network are working except one. This filter allows you to perform targeted investigation and speed up the overall troubleshooting workflow since you are not distracted by unnecessary data.
To capture packets related to a specific host, set the host’s network address with the host setting:
sudo tcpdump -c 5 host 192.168.2.1Similar to the network protocol filter, this command will only return output if an ongoing transmission is bound to the defined host.
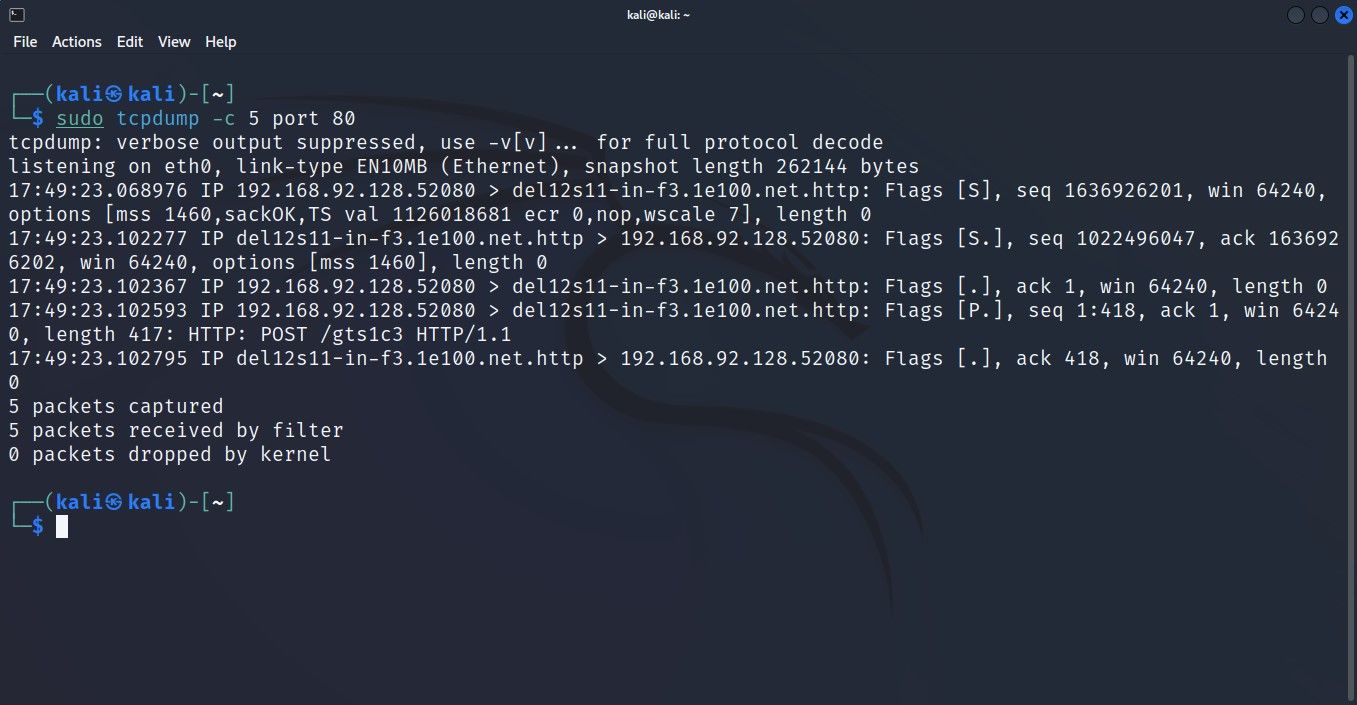
Filter packets based on active port
tcpdump is equipped with a parameter that allows you to filter network traffic and capture only packets transmitted to or from a specific port.
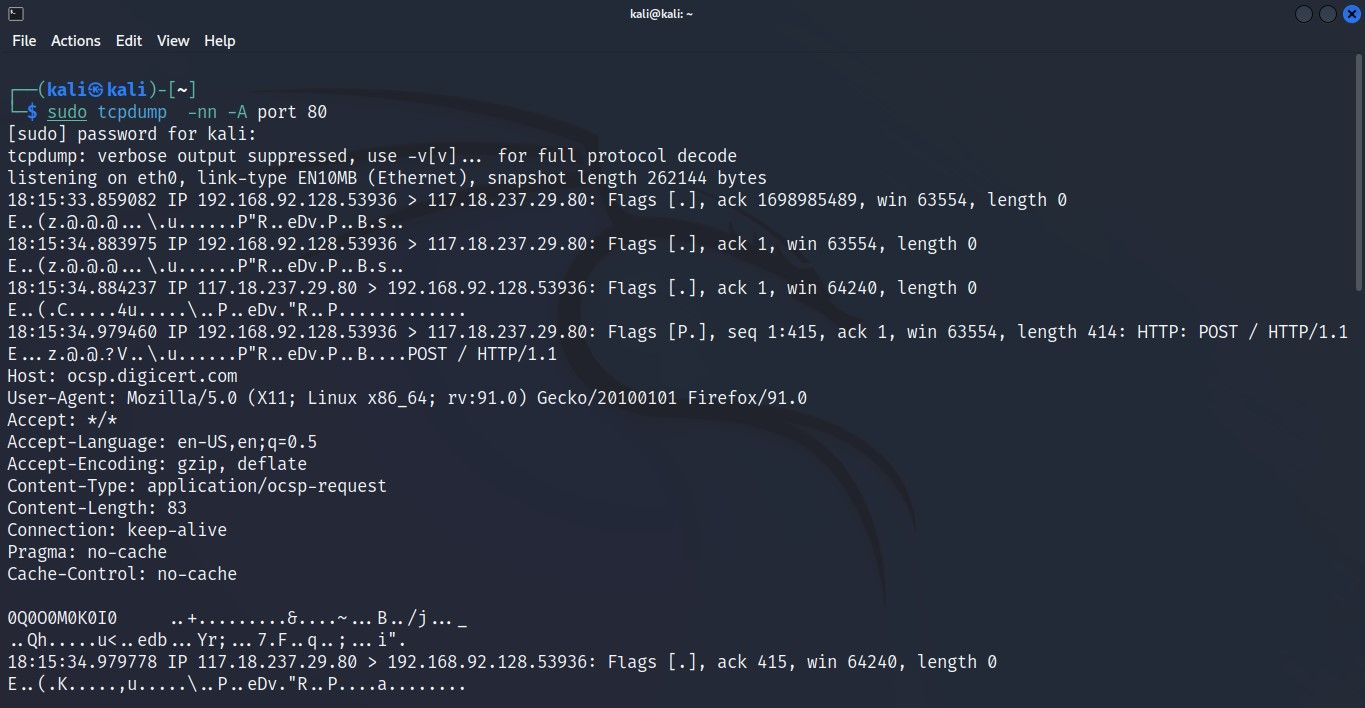
To capture packets from a specific port, add the Port flag to the tcpdump command and set the port number next to it. For example, to capture all incoming or outgoing HTTP traffic, set port 80:
sudo tcpdump -c 5 port 80
tcpdump will listen on port 80, waiting for HTTP transmissions. Once it detects HTTP packets on the network, it captures them.
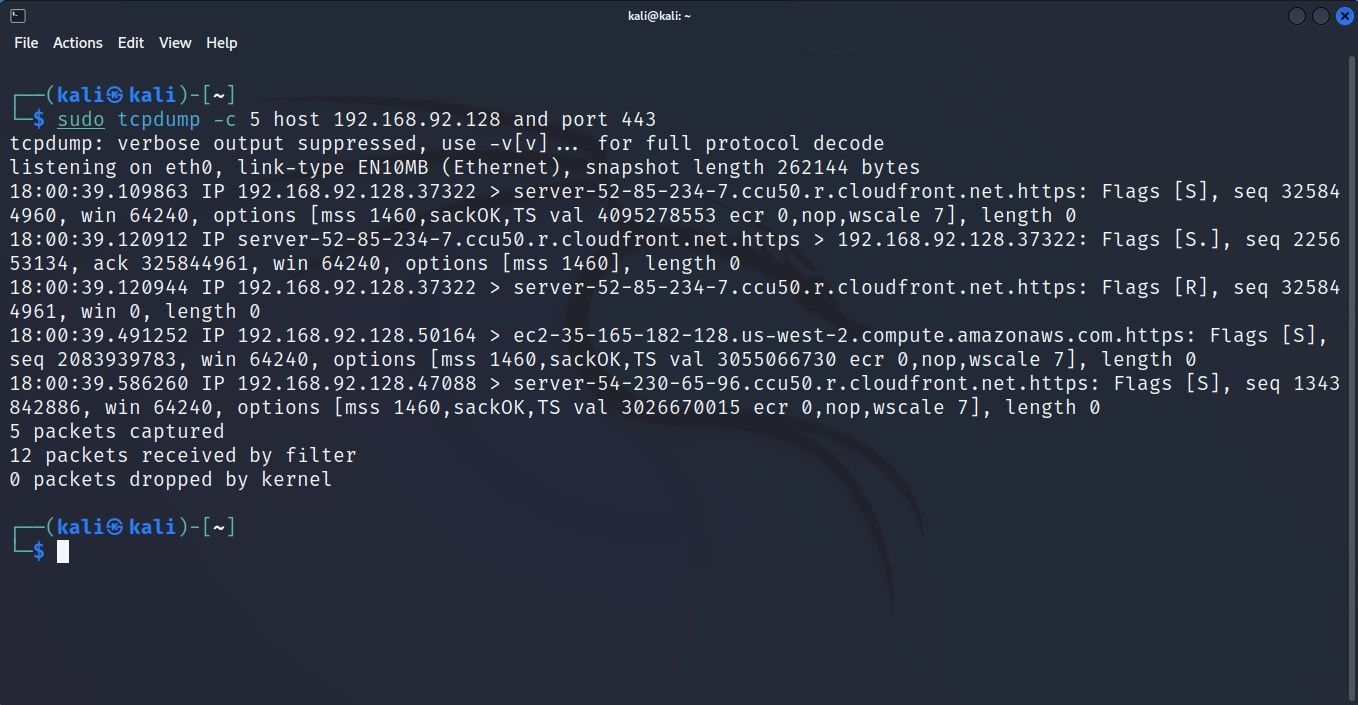
Combine filters together for advanced sorting
The previous sections have explained how you can filter traffic based on port, protocol, or host, but what if you want to capture traffic from a single port of a specific host at the same time? using a particular network protocol? Well, you’re in luck because it’s possible, thanks to the ability to use logical operators with the tcpdump command.
To capture packets from an individual host using port 443, use this command:
sudo tcpdump -c 5 host 192.168.2.1 and port 443
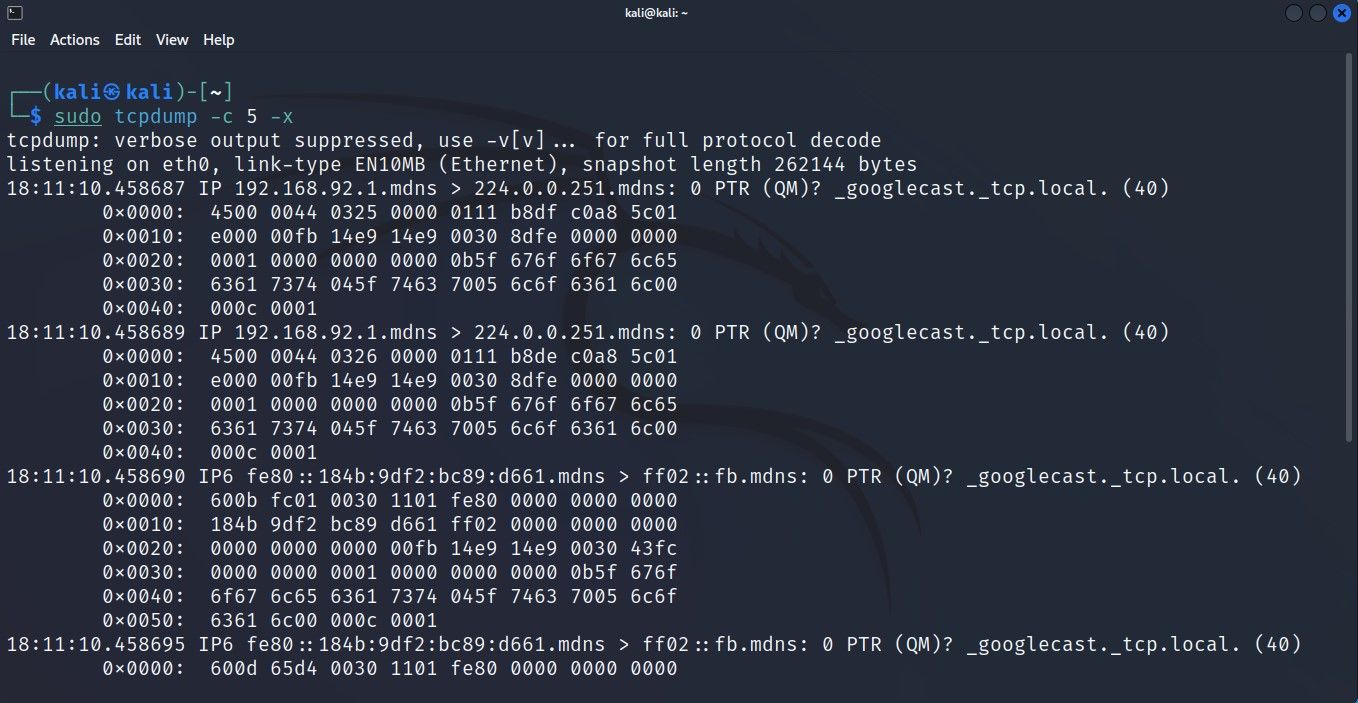
Inspect the contents of captured packets
By default, tcpdump displays packet headers in the output. While this is more than enough in most cases, sometimes you want or need to dig deeper into the captured data. You can pass some parameters with the tcpdump command to inspect the contents of the captured package.
Here is how to display the contents of packages:
sudo tcpdump -c 5 -xThis command returns the hexadecimal version of the content in a captured packet. If you want to view the ASCII form of the data, you can pass the -A parameter with:
sudo tcpdump -ASave tcpdump output to a file
Like almost any other Linux command line tool, you can store the output produced by tcpdump in a file to be referenced later.
This can be done by adding the -w flag at command. When running, tcpdump will store captured data in a .pcap file that can be analyzed later with tcpdump or other network monitoring tools like Wireshark.
Type this command to store the output of your tcpdump command to a file:
sudo tcpdump -w capture.pcapTo read a .pcap file, you can use tcpdump with the -r setting:
sudo tcpdump -r capture.pcapLinux comes with a plethora of networking tools that can fix all networking issues as long as they are on the software side. Knowing how to use some of the best networking tools in Linux will definitely come in handy, whether you’re a system administrator running networks for a living or just an everyday Linux user.
Since the actual list of network commands available may be too difficult to understand, here is a list of some of the most important Linux network tools you should know.