A new Linux vulnerability known as the “Dirty Pipe” allows local users to gain root privileges through publicly available exploits.
Today, security researcher Max Kellermann responsibly disclosed the “Dirty Pipe” vulnerability and said it affects Linux kernel 5.8 and later, even on Android devices.
The vulnerability is identified as CVE-2022-0847 and allows an unprivileged user to inject and overwrite data into read-only files, including SUID processes that run as root.
Kellerman discovered the bug after tracking down a bug that corrupted web server access logs for one of his clients.
Kellerman states that the vulnerability is similar to the Dirty COW vulnerability (CVE-2016-5195) patched in 2016.
Public exploits give root privileges
As part of the Dirty Pipe disclosure, Kellerman released a proof-of-concept (PoC) exploit that allows local users to inject their own data into read-only sensitive files, removing restrictions or changing configurations to provide wider access than they usually would. .
For example, security researcher Phith0n illustrated how they could use the exploit to modify the /etc/passwd file so that the root user doesn’t have a password. Once this change is made, the unprivileged user could simply run the ‘su root‘ to access the root account.
Why did I overwrite /etc/passwd?
Because this file saves all user information on Linux.
I remove the “x” flag behind the “root” user, it means I have set an empty password for this user. So I can use “su root” to elevate privileges without credentials.— Phith0n (@phithon_xg) March 7, 2022
However, an updated exploit released today makes it even easier to gain root privileges by patching the /usr/bin/su command to drop a root shell at /tmp/sh and then running the script.
Once executed, the user gains root privileges, as shown below in BleepingComputer in Ubuntu 20.04.3 LTS running generic kernel 5.13.0-27.
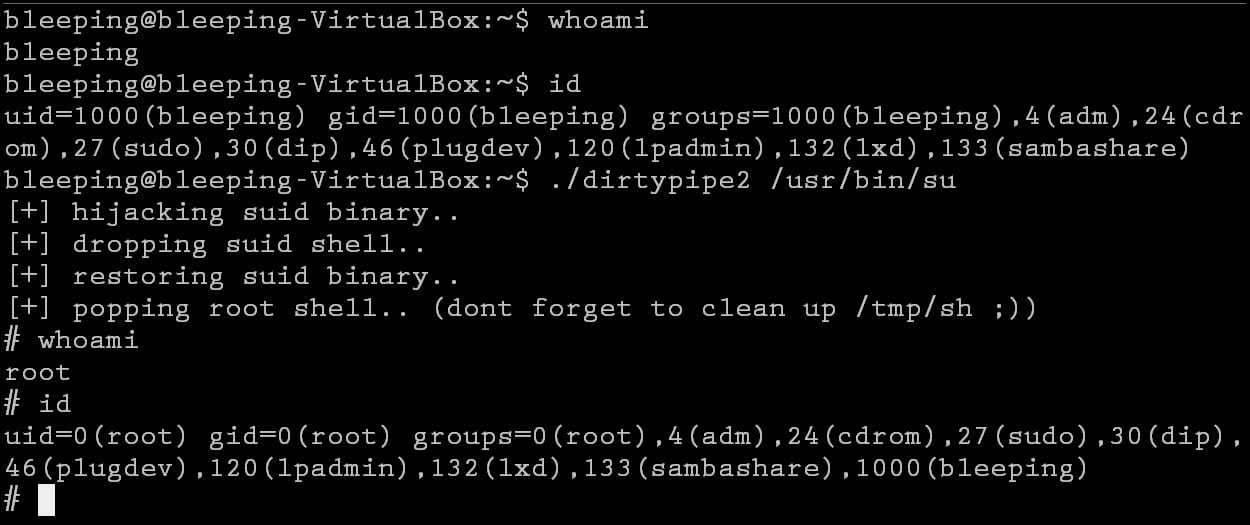
Source: BleepingComputer
The vulnerability was responsibly disclosed to various Linux maintainers as of February 20, 2022, including the Linux Kernel Security Team and the Android Security Team.
Although the bug was fixed in Linux kernels 5.16.11, 5.15.25, and 5.10.102, many servers continue to run outdated kernels, making the release of this exploit a significant issue for administrators. server.
Additionally, due to the ease of gaining root privileges using these exploits, it is only a matter of time before threat actors start using the vulnerability while conducting attacks. attacks. The similar Dirty COW vulnerability was previously used by malware, although it was harder to exploit.
This bug is of particular concern to web hosting providers that offer Linux shell access or universities that typically provide shell access to multi-user Linux systems.
It’s been a rough year for Linux, with many high-level elevation of privilege vulnerabilities exposed.
These include elevation of privilege vulnerabilities in the Linux iSCSI subsystem, another kernel bug, the Berkeley Extended Packet Filter (eBPF), and Polkit’s pkexec component.