[ad_1]
A pair of Linux kernel vulnerabilities disclosed this week exposes major Linux operating systems that could allow a hacker to gain root privileges on a compromised host or shut down the entire operating system completely.
The two flaws – CVE-2021-33909 and CVE-2021-33910, respectively – were disclosed by vulnerability management vendor Qualys in a pair of blogs describing the threat to these Red companies’ Linux operating systems. Hat, Ubuntu, Debian, and Fedora.
The vulnerabilities arose the same week that a flaw in Microsoft’s Windows 10 operating system – one that impacts the Security Account Manager functionality and has been dubbed “SeriousSAM” – emerged that could also allow an attacker to bypass operating system security restrictions and gain access to data on a compromised system (see Microsoft Security Under Control After Recent Incidents).
In both cases, the vulnerabilities in Linux and Windows operating systems were discovered by security researchers rather than malicious actors, and patches or workarounds were recommended for everyone. However, they once again highlighted flaws that can be found buried in operating systems that could lead to big headaches if exploited by bad actors.
In the case of Linux vulnerabilities, security researchers at Qualys have recommended that users of various Linux distributions apply patches.
Further Reading: Key Vulnerability Management Tools for 2021
Red Hat, others confirm flaws
In an advisory, Red Hat officials acknowledged the flaw that could allow attackers to crash a compromised system and said any product based on the Red Hat Enterprise Linux kernel – including OpenShift Container Platform, OpenStack, and Red Hat Virtualization – could be affected.
“This flaw allows a local attacker with user privilege to access out-of-bounds memory, leading to a system crash or an internal kernel information leak,” the IBM company wrote. “The problem is the result of not validating the conversion of size t to int before performing operations. The greatest threat from this vulnerability is data integrity, confidentiality, and system availability.
Other major Linux distributors, including Debian, Ubuntu, and SUSE, have also confirmed the CVE-2021-33909 vulnerability.
A silver lining
Shawn Smith, director of infrastructure at application security provider nVisium, said ESecurity planet that while the vulnerabilities are serious, the silver lining is that both require an attacker to be an authorized local user.
“By itself, this will not give a remote attacker access to anything, but if combined with other attacks, it is possible that an attacker could exploit a user account from elsewhere and pivot on it to get root access, â€Smith said. “Linux security is a pretty big topic because there are so many different forks that fall under the Linux ecosystem, but overall it’s a pretty secure system. Because it is open source, anyone can conduct code audits and many issues are detected before they are merged into main, but sometimes bugs like this slip away and can go undetected for months or even years.
Find Linux vulnerabilities
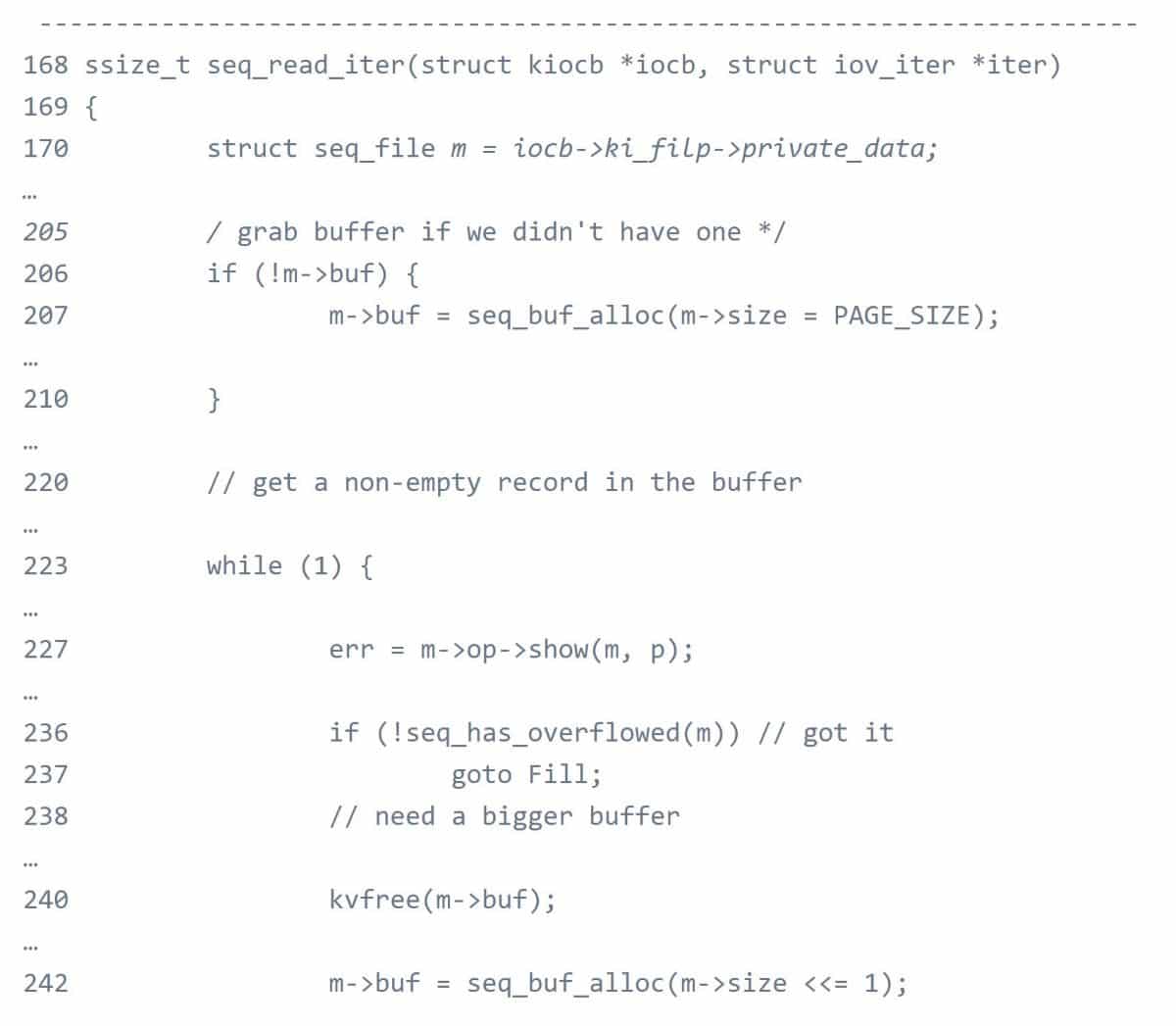
The issue Red Hat referred to is a size t to int conversion vulnerability in the kernel file system layer, according to Qualys. By exploiting the vulnerability in a default configuration, an attacker could gain root privileges on a vulnerable host.
The file system includes data and metadata on a storage device, controlling how data is stored and retrieved, and managing user data.
“The Linux file system interface is implemented as a layered architecture, separating the user interface layer from the implementation of the file system and the drivers that manipulate storage devices,†Bharat Jogi wrote. , senior manager of vulnerabilities and signatures for Qualys, in a blog. Publish. “It is the most important function of any operating system and it is ubiquitous on all major Linux operating systems. “
Jogi wrote that Qualys was able to develop an exploit and gain full root privileges on default installations of Ubuntu 20.04, Ubuntu 20.10, Ubuntu 21.04, Debian 11 and Fedora 34 Workstation, adding that “other Linux distributions are likely vulnerable and probably exploitable “.
The other issue was a stack exhaustion denial of service vulnerability in systemd (PID 1), a utility in major Linux distributions that an attacker could exploit to crash systemd and, therefore, the entire systemd. operating system. Systemd includes a range of components for Linux operating systems, according to Jogi. The vulnerability was introduced in systemd v220 in April 2015.
“Serious potential”
Dirk Schrader, global vice president of security research at change management software provider New Net Technologies, said ESecurity planet that while vulnerabilities are unlikely to be part of malware campaigns, they have “high potential when used in a coordinated and targeted attack scenario.” Both seem to need an already existing user account on a targeted device, which seems like a surmountable hurdle with all the credentials leaked in the recent past. Here’s how big data can be used in cybercrime.
Businesses shouldn’t ignore these vulnerabilities.
“The reason businesses should be concerned is that Linux devices are typically found in the world of infrastructure servers, with systems being critical to a company’s operations,†said Schrader. “Organizations won’t want their operations disrupted (CVE-2021-33910) or taken over and controlled by an attacker (CVE-2021-33909) with the ability to do anything.
“Noisy” vulnerabilities
According to Joseph Carson, chief security scientist and chief information security advisory (CISO) at cloud identity solutions maker ThycoticCentrify, companies need to take the threat seriously, but noted that these vulnerabilities are noisy, which makes them easy to detect if an attacker tries to exploit them. That said, companies would be wise to reduce risk by ensuring that affected systems are not publicly exposed to the Internet or that they are protected using solutions such as Privileged Access Management (PAM).
“Like any operating system, security is completely dependent on how you use it, configure or manage the operating system,†Carson said. ESecurity planet. “Every new Linux update tries to improve security; however, to get the value, you must enable and configure it correctly. The state of Linux security today is quite good and has evolved in a positive way, with more visibility and built-in security features, although like many operating systems you need to install it, the configure and manage it with security in mind because how cybercriminals take advantage of it is the human touch.
[ad_2]